What Ransomware is
Ransomware or Crypto-Malware" is defined as all those programs or software that block access to files or computers by demanding a cash ransom to access them. Crypto-Malware is designed to make the computer or files unusable by encrypting them, with the aim of extorting money from the victim by forcing her to pay a ransom suitable for obtaining the decryption keyHeuristic Behavioural Technologies
The signature method for these types of attacks, is ineffective in many cases as carrier files are artfully modified on an hourly basis or less to evade their identification by classic signature/pattern methods.For this reason, the interception of the attack is desirable to occur not only through prior identification of the carrier files but supplemented with heuristic behavioral technologies that are capable of signaling the attack in its early stage, should the carrier file not be recognized by the signature method.

As of May 2015, Anti-Ransomware Crypto-Malware protection technologies have been implemented in Vir.IT eXplorer PRO antivirus to mitigate this type of attack, so as to safeguard document files from encryption. These technologies developed by the authors of Vir.IT eXplorer PRO can recognize the encyption process in progress, blocking it in its initial stage.
Vir.IT Anti-Ransomware technologies Crypto-Malware protection
Vir.IT eXplorer PRO's Anti-Ransomware protection monitors the main types of document files (doc, xls, pdf, jpg, etc.), and in case these files should be encrypted, as soon as the predefined maximum threshold is exceeded, Anti-Ransomware technologies intervene by inhibiting file access to the encryption process in progress. Saveguarding PC and SERVER document files.

Based on October 2015 statistics, the effectiveness of Anti-Ransomware technology integrated into Vir.IT is 99.63%, which is the average percentage expectation of files saved from encryption by Vir.IT.
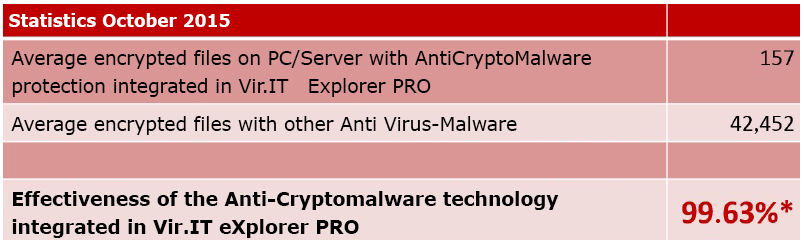
* Average percentage expectation of saved files from encryption thanks to Vir.IT eXplorer PRO antiransomware protection: Reference calculation details
It has been field verified that the effectiveness of heuristic behavioral technologies Anti-Ransomware Protection Crypto-Malware in its best performance is able to block the attack after the encryption of the first 5 files.
If the user uses Vir.IT eXplorer PRO in accordance with the technical specifications of use, on average in absolute terms, the number of encrypted files in the initial stage will be limited to around ten.
For the recovery of the few files encrypted in the initial stage, Vir.IT eXplorer PRO has the following encrypted files recovery/restoration technologies:
If the user uses Vir.IT eXplorer PRO in accordance with the technical specifications of use, on average in absolute terms, the number of encrypted files in the initial stage will be limited to around ten.
For the recovery of the few files encrypted in the initial stage, Vir.IT eXplorer PRO has the following encrypted files recovery/restoration technologies:
- Private key Recovery
- Backup On-The-Fly
- Vir.IT Backup

For some Ransomware types, the authors of Vir.IT eXplorer PRO, after thorough analisys have implemented a system that can identify the private encryption key used by Crypto-Malware in the attack.
With the availability of the private encryption key, using the tools in Vir.IT eXplorer PRO it will be possible to recover the few encrypted files in the initial phase of the attack without losing a single comma.
With the availability of the private encryption key, using the tools in Vir.IT eXplorer PRO it will be possible to recover the few encrypted files in the initial phase of the attack without losing a single comma.
With this technology there is a reasonable expectation of recovering 100% of the files encrypted in the initial phase of the attack.
If it is not technically possible to seize the private key for the particular family/type of ransomware or its variant, the recovery of encrypted files in the initial phase can be done through Backup On-The-Fly technology.
If it is not technically possible to seize the private key for the particular family/type of ransomware or its variant, the recovery of encrypted files in the initial phase can be done through Backup On-The-Fly technology.

"Backup On-The-Fly" technology backs up document files of major types, ranging in size from 2 KB to 3 MB when the file is deleted or truncated, and stores them within a service folder for 48 hours.
This is a plus that allows through Vir.IT eXplorer PRO in case of Crypto-Malware attack, to restore most of the files encrypted during the initial phase of the attack.
This is a plus that allows through Vir.IT eXplorer PRO in case of Crypto-Malware attack, to restore most of the files encrypted during the initial phase of the attack.
As is the case with private key recovery, no changes are lost for files restored through "Backup On-The-Fly".
Any files not available for restoration from "Backup On-The-Fly" can be restored, as a last parachute, by Vir.IT Backup.
Any files not available for restoration from "Backup On-The-Fly" can be restored, as a last parachute, by Vir.IT Backup.
This is a technology integrated into the Vir.IT Security Monitor resident shield of the Vir.IT eXplorer PRO suite, not to be confused with "Backup On-The-Fly," made back in 2014 to specifically protect PC and SERVER data files from Ransomware / Crypto-Malware attacks, including next-generation attacks. Vir.IT Backup is to be considered an advanced backup system capable of preserving from encryption and/or deletion (even by a possible clumsy user) the generated backup files.
The effectiveness of Vir.IT Backup is, of course, contingent on its proper configuration done when Vir.IT eXplorer PRO is installed.
The effectiveness of Vir.IT Backup is, of course, contingent on its proper configuration done when Vir.IT eXplorer PRO is installed.
For more details on Vir.IT Backup's features, please see the policy at the following LINK


